
Despite the headlines, phishing and ransomware remains a disproportionate problem for small businesses. Recent reports show that 40% of ransomware attacks were against smaller companies with 1 to 100 employees. Small companies are much less likely to have adequate backups or the financial resources to make a full recovery following a ransomware attack.
Business Email Compromise (BEC)
Stay alert to emails which are the most common way that cyber criminals carry out a Business Email Compromise scam. These can include:
- Spoof emails of account or website. Slight variations on legitimate addresses can fool victims into thinking fake accounts are authentic.
- Phishing emails. These messages look as if they are from a trusted sender to trick victims into revealing confidential information or wiring money to a fraud account.
- Malware. Malicious software can infiltrate company networks and gain access to legitimate email threads and let criminals gain undetected access to data, including passwords and financial account information.
- Ransomware is often spread through phishing emails that contain malicious encryption attachments or downloads malware without the user’s knowledge.
Cyber Insurance
The spike in cybercrime has driven demand for cyber insurance policies specifically designed for small businesses. Our Agents offer coverage to protect your American dream. Premiums are as low as $200 when endorsed to many Business Owners Policies (BOPs) and Commercial Package Policies or may be purchased as stand-alone Cyber Policies.
Standalone Cyber Policies contain third party liability (violations of customer protected info) and expanded coverages for first party losses (to your business operations) like crisis management, fraud response, public relations, forensic and legal expense, extortion and ransomware loss, social engineering and funds transfer fraud, telecommunications theft, system disruption business interruption, data recovery expense, network disruption, funds transfer fraud, and more.
To get a free cyber quote - CONTACT US, visit either office, or email Quotes [at] Am-Ins [dot] com.
REAL EXAMPLE
As I was writing this article, this real-life example of a phishing email was received by my employee. The fraud indicators for your employees to watch for are: Even though my name is shown as the email sender, the email address is not mine. Next, the tone and grammar is off..."I'll need you (to) run a quick task"... the missing "to" is a grammar indicator and the tone and style of the email doesn't match what an employee would expect to receive from me.
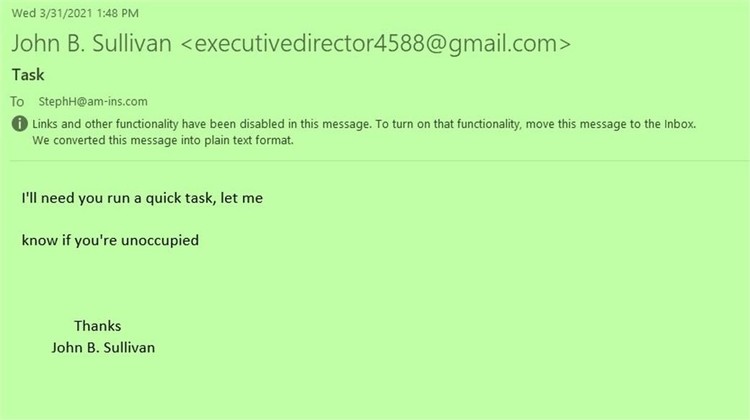
Scam emails can be obvious or they can appear just like a true note when they are appearing to come from an actual fellow staff member inside your office.
If my employee had responded to this email, the phishing criminal would have tried to real-us-in with an attachment containing malware or a scam to get money sent to a fake account. Don't respond or open any attachments. Get IT help if needed.


